Claude Code's Source Leak: What Happened and What Teams Should Learn
We had a different article planned for today. We bumped it because Anthropic's Claude Code source leak is a better lesson for engineering teams: release engineering mistakes can become public security events in a single publish.
Jason Overmier
Innovative Prospects Team
We had a different article planned for April 1, 2026. We pushed it back because Anthropic’s Claude Code leak is more useful to study while the details are still fresh.
This incident matters for two reasons. First, Claude Code is one of the highest-profile AI engineering tools on the market, so its release process should be among the better ones in the industry. Second, the failure mode was painfully normal: not a cinematic intrusion, but a release packaging mistake.
We are also going to stay disciplined here. We are not linking to the leaked archive, and we are not repeating every viral claim about hidden features. The useful part of this story is the operational lesson, not the gossip.
What Is Verified as of April 1, 2026
The clearest facts come from public npm infrastructure and Anthropic’s statement to Axios.
- The npm registry metadata for
@anthropic-ai/claude-coderecords version2.1.88as published on March 30, 2026 at 22:36:48.424 UTC and version2.1.89as published on March 31, 2026 at 23:32:40.530 UTC. - As of April 1, 2026, the direct npm version endpoint for
2.1.88returns404, while the package metadata still showslatestandnextpointing to2.1.89, consistent with2.1.88being the withdrawn release and2.1.89being the replacement. - Axios reported on March 31, 2026 that a debugging-related file was accidentally bundled into a routine Claude Code update, pointing to an Anthropic-hosted archive containing nearly 2,000 files and roughly 500,000 lines of code.
- Anthropic told Axios this was “a release packaging issue caused by human error, not a security breach” and said no sensitive customer data or credentials were exposed.
Those facts support a narrow but important conclusion: this was a release artifact exposure, not a confirmed compromise of Anthropic’s internal systems.
What We Should Not Overclaim
There are already plenty of viral claims about every hidden feature, model codename, and internal system allegedly visible in the leaked material.
Some of those claims may be accurate. Some may be embellished. Because the reported bad release, 2.1.88, is no longer available from the normal npm version endpoint, not every detail can still be independently verified from first-party infrastructure.
Just as important, the public reporting does not give us enough evidence to say with confidence whether the exposed material came from a source map, a debug bundle, a generated manifest, or some other packaging mistake. What we can say is simpler and more defensible:
- a public package was published
- the package included internal material that should not have been public
- the package was superseded quickly, but not before others copied it
That is already enough to learn from.
What This Incident Actually Teaches
The real lesson is not “AI companies move too fast.” The real lesson is that the release artifact is a security boundary.
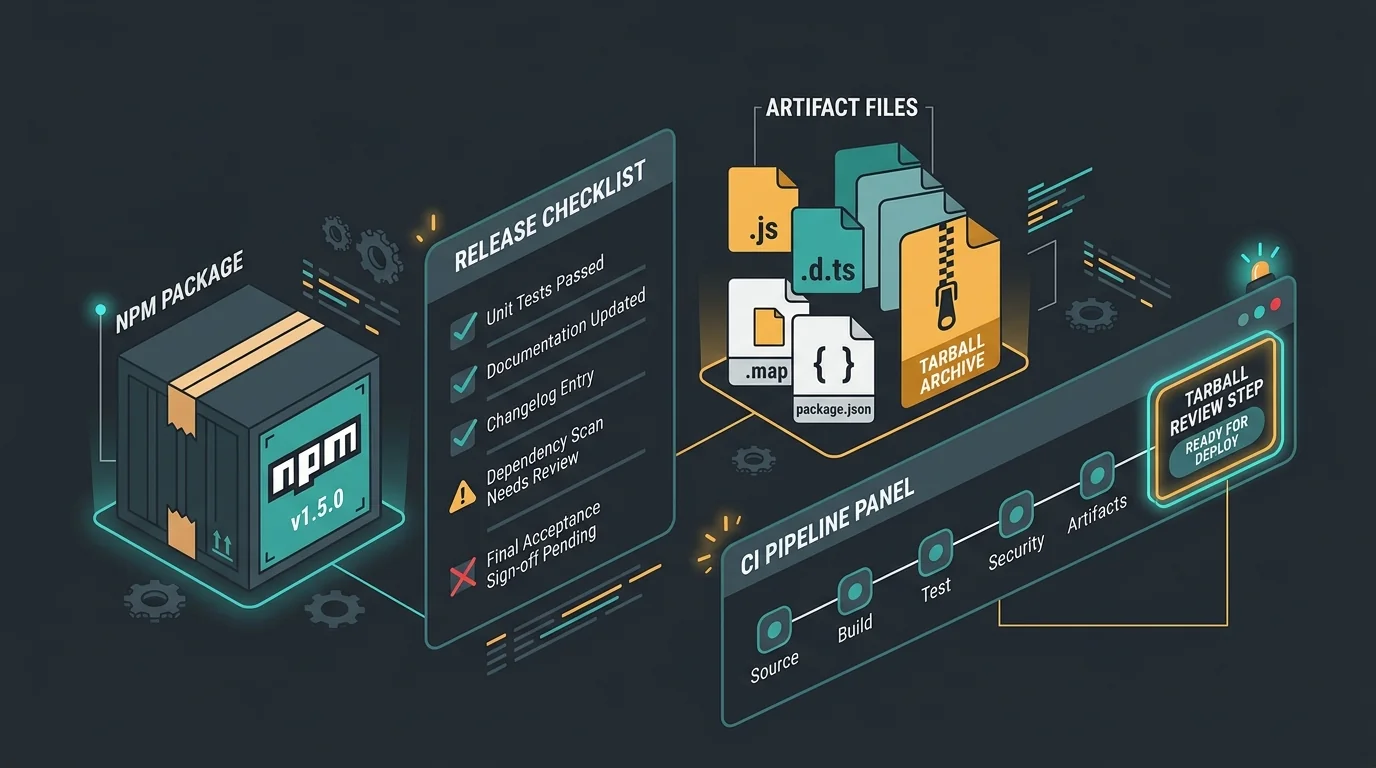
Teams still spend too much time reviewing repository code and too little time reviewing the exact tarball, bundle, container image, or installer that leaves CI. npm’s own documentation is blunt about how easy it is to ship too much by accident:
- The
filesfield inpackage.jsonis an inclusion list for the published tarball. - If you omit
files, npm defaults to["*"], meaning it will include all files unless something else excludes them. npm packexists specifically to create the tarball you are about to ship.npm pack --dry-runreports what npm would publish without actually publishing it.npm diffcan compare the current package directory against the latest published package or compare two published versions directly.
That combination makes the operational failure mode here painfully recognizable. A package got built, packed, and published without a final gate asking the only question that matters: “Is this exact artifact safe to make public?”
Source Maps Are a Policy Decision, Not a Harmless Default
We should be careful not to claim that source maps caused this specific Claude Code incident unless Anthropic confirms that. But source maps are still part of the broader lesson because too many teams treat them as low-risk by default.
The tradeoff is not hypothetical:
- Chrome DevTools documentation explains that source maps let tools load and debug your original files alongside the deployed code.
- Next.js keeps production browser source maps disabled by default specifically to prevent “leaking your source on the client.”
- The same Next.js documentation notes that when you enable production browser source maps, they are written next to the JavaScript files and served automatically when requested.
That does not mean all source maps are bad. It means every team needs an explicit policy:
- browser app debugging may justify them
- CLI packages usually do not
- server bundles usually do not
- proprietary desktop tools usually do not
If the rule is not explicit, the default becomes “whatever the build tool emitted.”
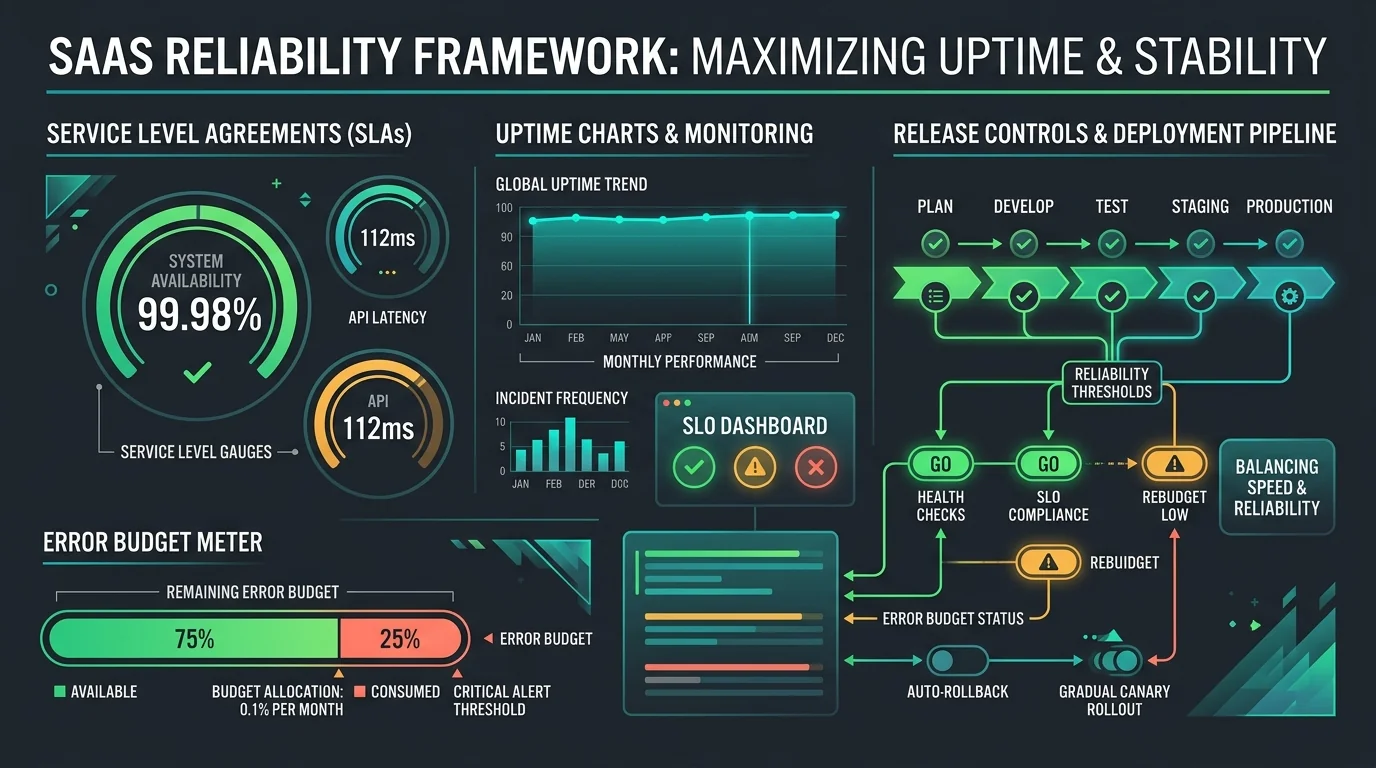
Why Fast Containment Does Not Undo Exposure
One of the most important takeaways is that rollback is not the same thing as erasure.
npm’s Unpublish Policy explains two things that matter here:
- registry data is immutable once published
- unpublishing is allowed only under specific conditions, including a limited 72-hour window for newly created packages
Even when a bad version disappears from the normal endpoint quickly, that does not mean nobody retrieved it. Public registries, mirrors, security researchers, and downstream users move fast. The window between “published” and “copied elsewhere” can be minutes.
That is why containment has to start before publication with artifact controls, not after publication with cleanup messaging.
What We Would Change in a Real Release Pipeline
This is the practical checklist we would hand an engineering team after an incident like this.
| Control | Why it matters |
|---|---|
Require an explicit files allowlist | npm defaults are broader than many teams assume |
Run npm pack --dry-run --json in CI | Shows exactly what would be published before the publish step |
| Fail the build on forbidden patterns | Block .map, .env, fixtures, local docs, debug payloads, and archive files unless explicitly allowed |
| Diff the candidate package against the latest release | npm diff catches unexpected new files before users do |
| Publish only from CI, not developer laptops | Reduces local-state drift and makes publish behavior reproducible |
| Use trusted publishing with OIDC | npm recommends this to avoid long-lived write tokens in release workflows |
| Preserve provenance for every release | npm provenance can link a published package back to its workflow, commit, and build file |
That last pair matters more than many teams realize. npm’s trusted publishing documentation recommends publishing directly from CI with OIDC rather than long-lived write tokens, and npm’s package provenance documentation shows that published packages can expose build environment, workflow, source commit, and transparency-log details for auditing.
Those controls will not stop every mistake. But they dramatically improve your odds of catching a packaging failure before it becomes public.
Why This Matters Beyond Anthropic
Too many engineering teams still think of source leaks as a perimeter-security problem. Increasingly, they are a software-supply-chain problem.
The risky places are:
- npm, PyPI, and container registries
- CI artifacts
- sourcemap publishing rules
- crash-report uploads
- debug endpoints
- internal docs accidentally bundled with release output
That matters even more now that AI tools are speeding up shipping. Faster release cycles are great until they outpace artifact discipline.
A Better Postmortem Question
The weak version of this postmortem is “How did a smart company make an embarrassing mistake?”
The better version is:
- What was the last irreversible step before publication?
- Which automated control should have failed before that step?
- Who reviewed the shipped artifact itself rather than the source repository?
- How quickly can we identify, supersede, deprecate, and communicate a bad release?
Those questions help teams improve their systems instead of just enjoying someone else’s bad day.
The Bigger Lesson for AI Tooling
Anthropic is hardly the only company moving fast on AI developer tools. But that makes the lesson more important, not less.
AI vendors are increasingly asking customers to trust them with codebases, terminals, credentials, issue trackers, CI systems, and sometimes production-adjacent workflows. In that world, release engineering mistakes are not minor hygiene issues. They are trust events.
A company can have strong model safety research and still get burned by ordinary software operations. That is not a contradiction. It is a reminder that mature engineering requires both.
Our Take
The main lesson is not “never move fast.” It is “treat the exact thing you ship as a security boundary.”
Artifact review, package diffing, forbidden-file scans, provenance, and source-map policy are not glamorous controls. They are also the controls that stop routine updates from becoming industry-wide case studies.
That is why we changed today’s lineup.
If your team is adopting AI-heavy tooling and wants a sober review of release engineering, secrets hygiene, or supply-chain controls, talk with us. This is exactly the layer where fast-moving teams need adult supervision.