Production Hardening: Turning AI-Built Prototypes Into Shippable Products
AI can build prototypes in days, but shipping requires architectural judgment, testing, and infrastructure. Here's what separates demo from production.
Jason Overmier
Innovative Prospects Team
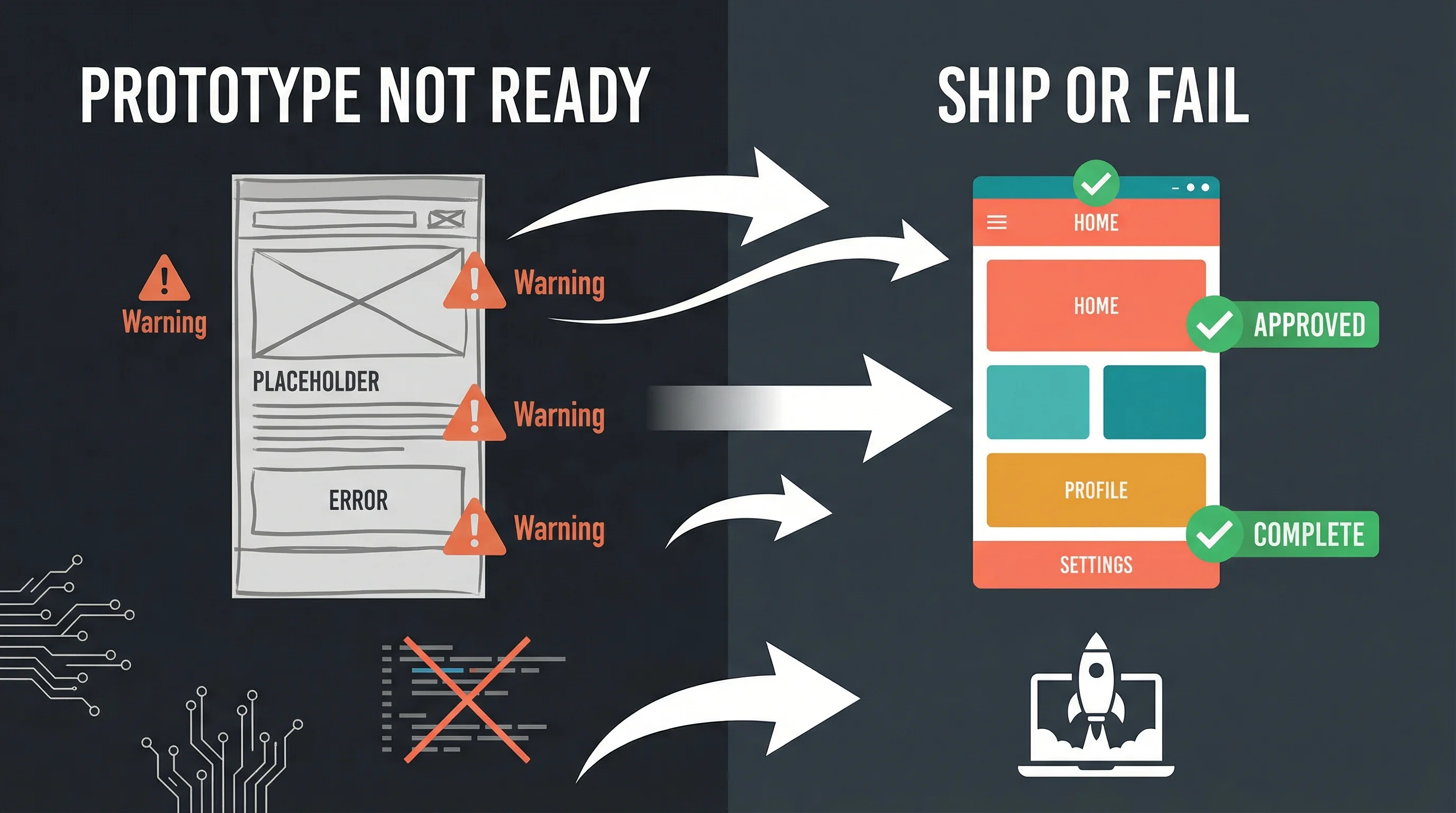
AI tools have compressed prototyping from months to days. A founder can now spin up a working app demo faster than ever before. But there’s a dangerous gap between “it works on my laptop” and “it handles real users at scale.”
Production hardening is the process of transforming AI-generated prototypes into shippable products. It’s not about making things prettier. It’s about architectural judgment, error handling, security, and infrastructure. The things that keep systems running when real users hit them with real data in the real world.
This article covers what production hardening actually entails, how to assess whether your prototype is ready, and when to bring in senior engineers to help bridge the gap.
The AI Prototype Gap
AI excels at generating code that works. What it doesn’t do: think about edge cases, plan for scale, anticipate failure modes, or make architectural trade-offs. These aren’t coding problems. They’re engineering problems.
A typical AI-built prototype might have:
- No error handling for API failures
- Hardcoded configuration values
- Missing input validation
- No rate limiting or abuse prevention
- Unclear data models that don’t scale
- Zero monitoring or observability
- Authentication bolted on as an afterthought
Each of these is a ticking time bomb in production. They won’t stop your demo from working. They will stop your product from working when it matters.
What Production Hardening Actually Is
Production hardening is systematic work across six dimensions:
1. Architecture & Data Models
AI generates code. Engineers design systems. The difference shows up in data models that accommodate future requirements, API contracts that version cleanly, and separation of concerns that enables independent scaling.
What this looks like:
- Normalized database schemas with proper indexing
- Clear API boundaries with versioning strategy
- Authentication/authorization as a cross-cutting concern, not a wrapper
- Stateless services that can scale horizontally
2. Error Handling & Resilience
Production systems fail. Networks timeout, databases hit connection limits, third-party APIs go down. Hardened systems anticipate failure and handle it gracefully.
What this looks like:
- Retry logic with exponential backoff
- Circuit breakers for failing dependencies
- Graceful degradation when non-critical services fail
- Error boundaries that contain failures instead of cascading
3. Security & Compliance
Prototypes often skip security “for now.” Production requires security from day one. Adding authentication later is exponentially harder than building it in from the start.
What this looks like:
- Input validation on all endpoints
- SQL injection and XSS protection
- Proper secrets management (no hardcoded keys)
- Rate limiting and abuse prevention
- Compliance considerations for your industry (HIPAA, PCI DSS, SOC 2)
4. Testing Strategy
AI code often lacks tests. Production code requires tests at multiple levels. Not just unit tests, but integration tests that verify behavior across system boundaries.
What this looks like:
- Unit tests for business logic
- Integration tests for API endpoints
- End-to-end tests for critical user flows
- Load testing to verify performance under traffic
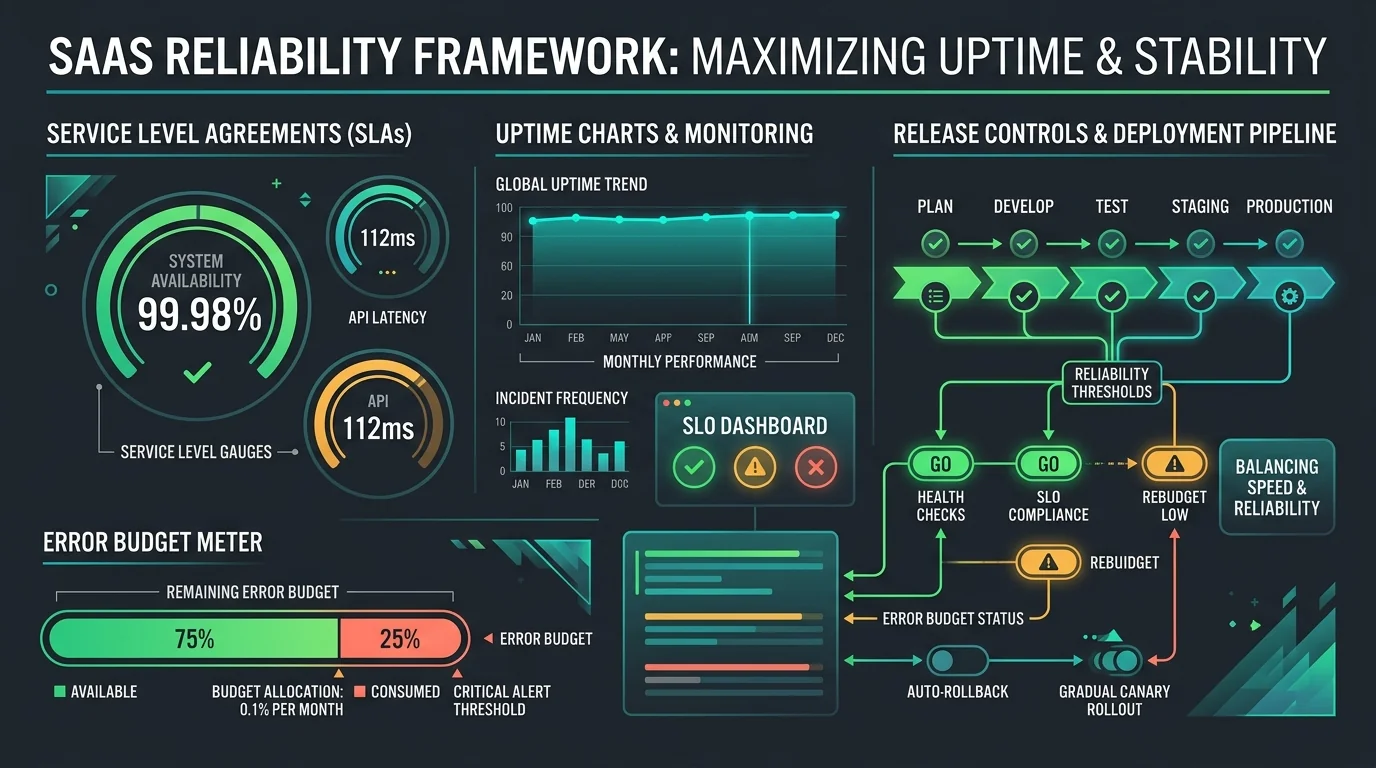
5. Observability & Monitoring
You can’t fix what you can’t see. Production systems need visibility into what’s happening, what’s failing, and what’s slow.
What this looks like:
- Structured logging with request IDs
- Metrics for latency, error rates, and throughput
- Alerts for actionable conditions
- Dashboards for system health
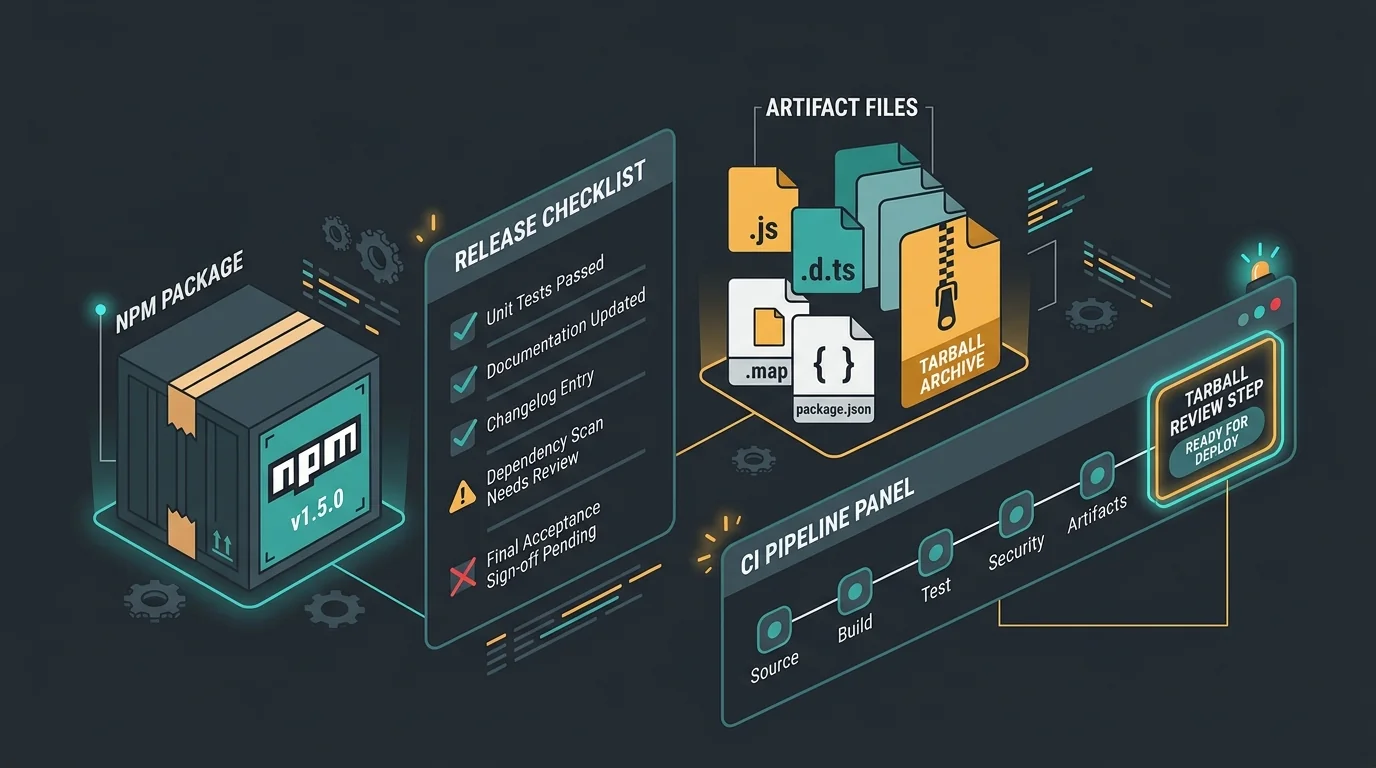
6. Infrastructure & Deployment
Code running locally isn’t code running in production. Hardened systems have deployment pipelines, environment management, and infrastructure that supports scaling.
What this looks like:
- Containerized applications
- CI/CD pipelines with automated testing
- Separate environments for dev, staging, production
- Infrastructure as code for reproducibility
The Hardening Checklist
Use this checklist to assess whether your prototype is production-ready. Each item is a potential blocker.
| Area | Check | Status |
|---|---|---|
| Architecture | Data model supports 10x growth | ⬜ |
| API versioning strategy documented | ⬜ | |
| Authentication integrated, not bolted on | ⬜ | |
| Error Handling | API failures retry with backoff | ⬜ |
| Database connection pooling configured | ⬜ | |
| Graceful degradation for non-critical features | ⬜ | |
| Security | All inputs validated before use | ⬜ |
| Secrets in environment variables, not code | ⬜ | |
| Rate limiting on public endpoints | ⬜ | |
| Testing | Critical paths have integration tests | ⬜ |
| Load test completed for projected traffic | ⬜ | |
| Security review completed | ⬜ | |
| Operations | Logging captures errors with context | ⬜ |
| Monitoring configured with alerts | ⬜ | |
| Deployment process documented and tested | ⬜ | |
| Compliance | Data retention policy defined | ⬜ |
| Privacy policy reflects actual data handling | ⬜ | |
| Industry-specific compliance addressed | ⬜ |
If you’re checking more than three boxes as “no,” you’re not ready for production. That’s not a criticism. It’s a reality check.
Common Pitfalls
| Pitfall | Why It Happens | Fix |
|---|---|---|
| Ship it now, fix later | Pressure to launch creates technical debt blind spots | Treat hardening as part of MVP, not a separate phase |
| AI-generated code is correct | Code runs successfully in development, so it must be production-ready | Assume all AI code requires security and edge case review |
| We’ll scale when we need to | Architectural decisions made early are expensive to change later | Design for 10x your expected initial traffic |
| Testing slows us down | Manual testing feels faster in the short term | Automated tests pay for themselves on the first production bug |
| Monitoring is for big teams | Small teams fly blind until users report problems | Start with basic logging and metrics from day one |
| Compliance is a legal problem | Engineers defer compliance to lawyers or ignore it entirely | Compliance requirements drive architectural decisions |
When to DIY vs Hire Help
Production hardening is a skill gap, not a knowledge gap. You can read about best practices, but applying them requires judgment that comes from experience. Here’s a framework for deciding when to bring in senior engineers.
DIY When:
- Your user base is friends and family (under 100 users)
- You have zero compliance requirements
- You’re comfortable debugging production failures at 2 AM
- The cost of downtime is zero
- You’re treating this as a learning project
Hire Help When:
- You’re handling real user data or payments
- You have compliance requirements (HIPAA, PCI DSS, SOC 2)
- You need to launch within a specific timeframe
- Downtime costs money or reputation
- You’re scaling beyond a single server
The middle ground is a production hardening engagement. Rather than building from scratch, senior engineers review your prototype, identify gaps, and implement the critical pieces. It’s faster and cheaper than a full rebuild, but more robust than crossing your fingers.
Cost/Benefit Analysis
Production hardening feels like overhead. It’s not. It’s insurance against expensive failures later.
Cost of hardening upfront: $10K-$50K depending on scope
Cost of post-launch failures:
- Emergency fix at 2 AM: $5K-$20K per incident
- Data breach from missing security: $50K-$500K depending on severity
- Rebuild from bad architecture: $100K+
- Lost customers from downtime: Unbounded
The math isn’t complicated. Hardening is cheaper than failure. The question is whether you pay now or pay later (with interest).
Timeline Reality Check
How long does hardening take? It depends on your prototype’s quality and your production requirements.
| Scope | Timeline | What’s Included |
|---|---|---|
| Basic Hardening | 2-3 weeks | Error handling, security basics, monitoring setup |
| Standard Hardening | 4-6 weeks | Plus infrastructure, testing strategy, deployment pipeline |
| Comprehensive Hardening | 8-12 weeks | Plus compliance, load testing, architecture refinement |
These timelines assume your prototype is functionally complete. If you’re still figuring out what you’re building, hardening should wait until product-market fit is clearer. You can’t harden a moving target.
The Hardening Process
If you decide to invest in production hardening, here’s what the process typically looks like:
Week 1: Assessment & Planning
- Architecture review and gap analysis
- Security audit of existing code
- Performance baseline measurement
- Prioritized hardening roadmap
Week 2-3: Critical Security & Stability
- Input validation and sanitization
- Secrets management implementation
- Error handling and retry logic
- Basic monitoring and alerting
Week 4-5: Testing & Deployment
- Integration test suite development
- Load testing and performance tuning
- CI/CD pipeline setup
- Staging environment configuration
Week 6: Launch Preparation
- Runbook creation for common issues
- Final security review
- Gradual rollout strategy
- Post-launch monitoring plan
Engagements can be compressed or expanded based on your timeline and risk tolerance.
AI has changed what’s possible for prototyping. It hasn’t changed what’s required for production. The gap between demo and shippable product is real, and crossing it requires engineering judgment that AI can’t provide.
Our team has hardened dozens of AI-built prototypes into production systems. We’ve seen what breaks, what leaks, what fails at 3 AM. We know how to bridge the gap efficiently without rebuilding from scratch.
If you have a prototype that needs production hardening, let’s talk. We’ll assess what you have, identify the gaps, and give you a roadmap to launch.