Secrets Management for Modern Development Teams
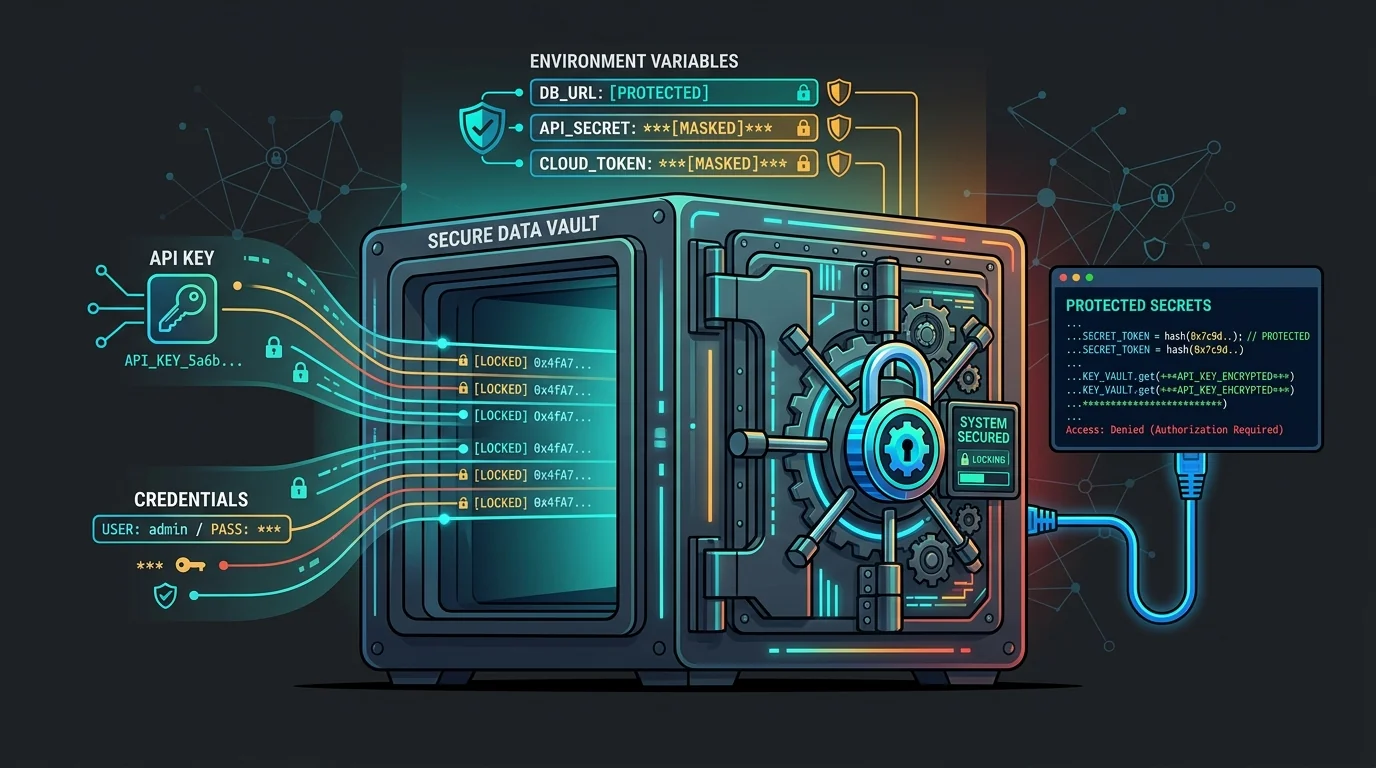
Credential leaks rarely happen because teams do not know secrets are important. They happen because the delivery process quietly teaches people unsafe shortcuts.
Jason Overmier
Innovative Prospects Team
Most secret-management failures are workflow failures.
Developers paste tokens into .env files, CI variables drift across environments, shared credentials survive far too long, and emergency fixes bypass the exact controls teams claim they care about. The answer is not just “use a vault.” The answer is to make the safe path the easy path.
Minimum Standard
| Control | Why it matters |
|---|---|
| Environment-specific secrets | Limits blast radius |
| Short-lived credentials where possible | Reduces long-term leakage risk |
| Rotation process | Makes incident response practical |
| Access logging | Helps teams investigate suspicious use |
| Secrets scanning | Catches accidental commits early |
Where Teams Still Leak Secrets
- copied config in screenshots or support threads
- hardcoded fallback tokens for local development
- CI systems with broad credentials shared across projects
- old credentials left active after a migration
- example files that are “temporary” for months
Those are process problems, not awareness problems.
Good Secret Hygiene for Delivery Teams
- Separate local, CI, staging, and production credentials.
- Prefer per-service or per-environment credentials over shared master keys.
- Treat rotation as routine maintenance, not just emergency work.
- Remove secrets from prompts, tickets, and chat logs.
- Audit which people and systems can actually read production secrets.
Common Pitfalls
| Pitfall | Why It Happens | Fix |
|---|---|---|
| One secret works everywhere | Convenience won early | Split by environment and service |
| Rotation breaks systems | Dependencies were undocumented | Inventory consumers before rotating |
| Secrets live in too many places | Tooling sprawl | Pick a primary source of truth |
| Teams trust policy over enforcement | Everyone “knows better” | Add scanners and access controls |
The Real Goal
Good secrets management should lower cognitive load. Developers should not have to improvise safe behavior every time they need to run a task, fix a deployment, or debug an integration.
If your controls only work when people remember them perfectly, they are not mature controls.
If you want to tighten secrets handling across environments and delivery workflows, contact us. We help teams reduce credential sprawl without slowing engineering to a crawl.