Software Handoff Checklist: Taking Over a Codebase from Another Team
The riskiest moment in many software projects is the handoff. Before you replace a vendor, absorb an acquired product, or move work in-house, make sure you know what is actually being transferred.
Jason Overmier
Innovative Prospects Team
The dangerous assumption in a software handoff is that code alone is enough.
A successful transition also requires environment access, deployment knowledge, monitoring context, support history, and a clear picture of where the system is fragile. If those things are missing, the receiving team inherits risk before it inherits momentum.
What a Real Handoff Includes
| Asset | Why it matters |
|---|---|
| Source code | The obvious part, but not the whole system |
| Infrastructure access | Without it, changes cannot be shipped safely |
| Secrets and credentials map | So access can be rotated cleanly |
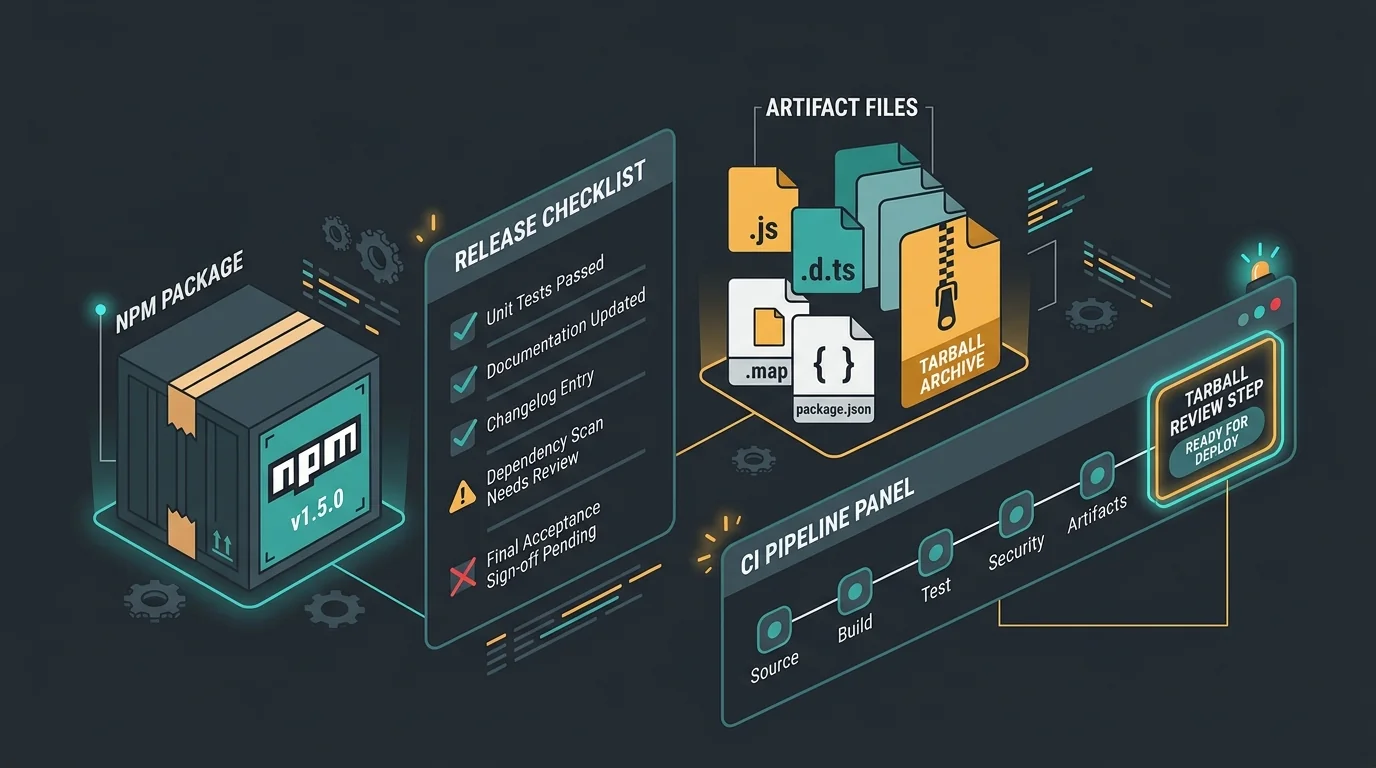
| Deployment workflow | So the new team can release without guesswork |
| Support and incident history | Reveals recurring weak spots |
| Architecture and dependency docs | Reduces onboarding drag |
Handoff Due Diligence Questions
Before accepting the handoff, ask:
- Can we deploy without the outgoing team present?
- Do we know which systems are business-critical?
- Is there enough automated test coverage to change the system safely?
- Do we understand where credentials live and who owns them?
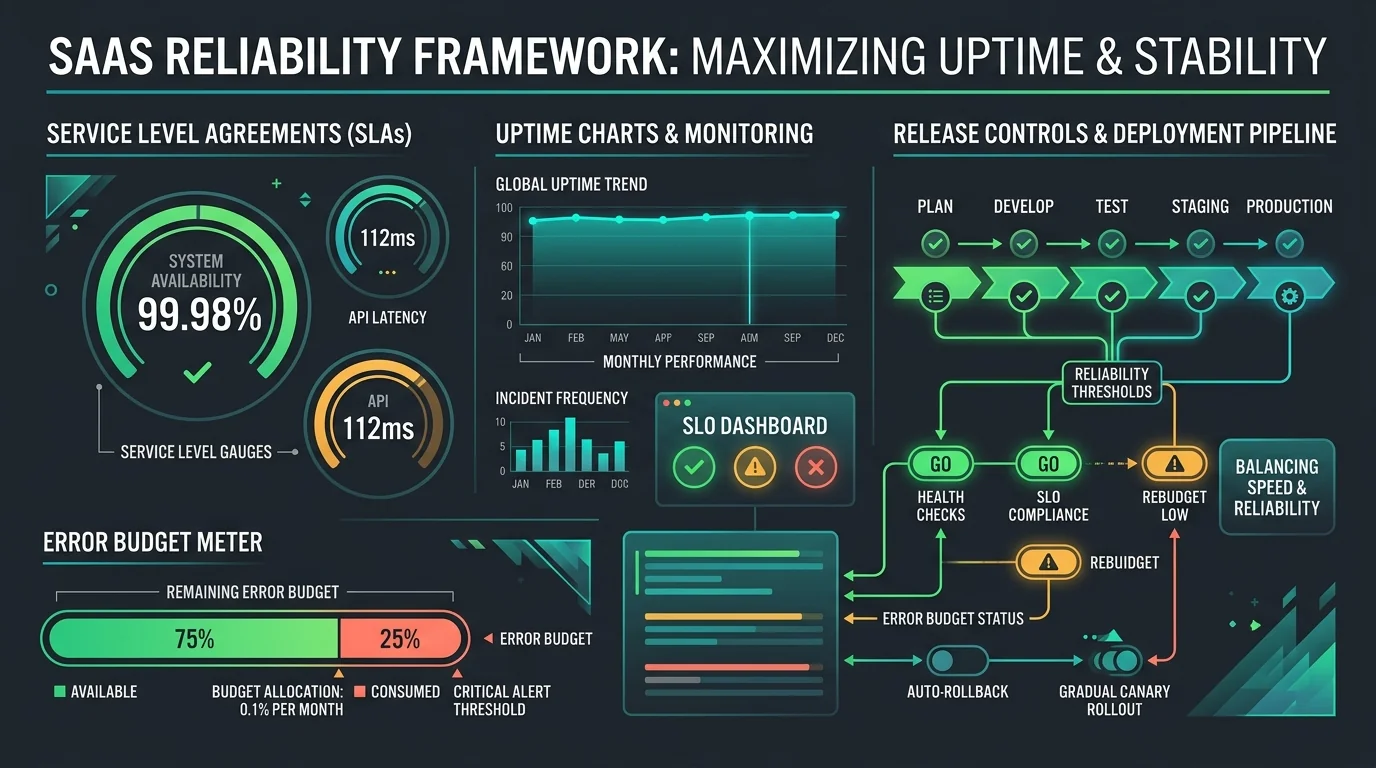
- Are monitoring, alerting, and logging already usable?
If the answer to several of those is no, the transition is incomplete.
Transition Plan by Phase
| Phase | Focus |
|---|---|
| 1. Inventory | Repos, environments, vendors, credentials, dashboards |
| 2. Access transfer | Accounts, permissions, and secret rotation plan |
| 3. Operational shadowing | Observe deploys, incidents, and support workflows |
| 4. Validation | Prove the new team can release and recover independently |
| 5. Stabilization | Prioritize the highest-risk gaps found during handoff |
This sequence prevents the new team from discovering the missing pieces during a production incident.
Common Pitfalls
| Pitfall | Why It Happens | Fix |
|---|---|---|
| Access gets transferred late | Everyone assumes it is administrative cleanup | Move access transfer earlier |
| Knowledge lives only in calls | Docs were never maintained | Require written runbooks and architecture notes |
| Old vendor remains a hidden dependency | The new team cannot operate alone yet | Define an independence milestone |
| Transition focuses only on code | Ops and support are ignored | Audit the full delivery system |
What Success Looks Like
A good handoff ends when the receiving team can:
- deploy confidently
- respond to routine incidents
- trace core dependencies
- prioritize stabilization work with real context
That is the point where the product is actually transferable.
If you are replacing a vendor or taking over an inherited codebase, contact us. We help teams run handoff audits, close operational gaps, and take control without freezing delivery.